Defend the Digital Frontier
The demand for cybersecurity experts has never been greater. Tomorrow needs digital defenders who can respond to emerging cyber threats with precision, speed, and skill.
Request Information
Form loading . . .
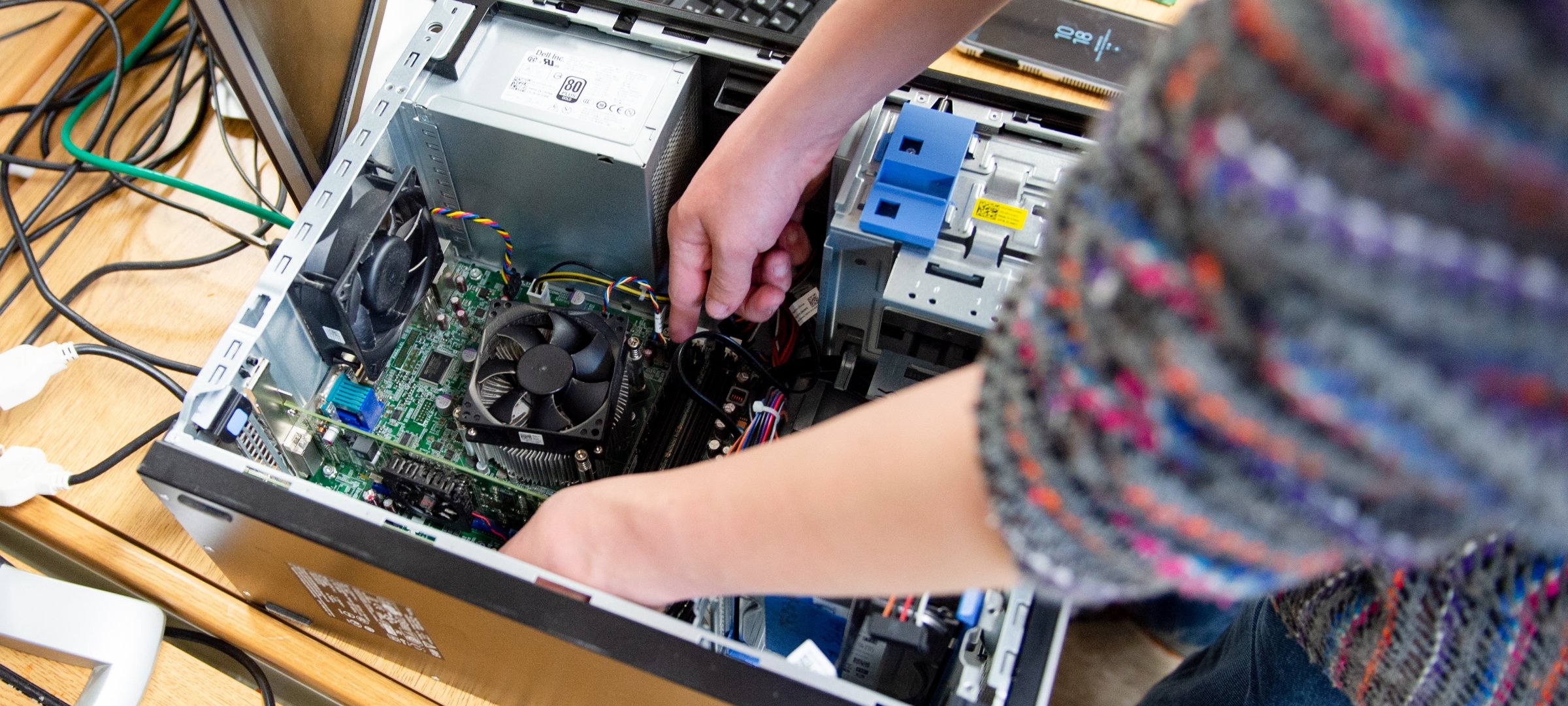
In the cybersecurity program at Michigan Tech, you'll make it your business to defend data, web, and communication systems from cyber-criminals, hackers, malware, and viruses. Play hack-and-defend "capture the flag" in class. Provide ethical hacking for real clients in the RedTeam student organization. Assess, plan, design, and implement cybersecurity defenses. You'll graduate ready for a rewarding, well-compensated career.
Customize your degree with one of two concentrations. With a concentration in software security, you'll focus on developing secure and trusted software systems and fixing vulnerabilities in existing software. With a concentration in system and network security, you'll focus on securing computer systems and networks within an enterprise environment from a range of internal and external threats.
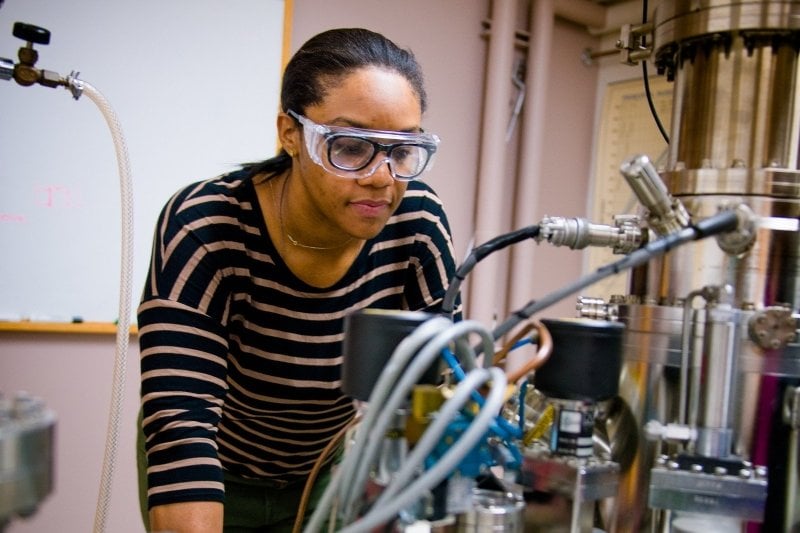
"The educational environment in the College of Computing at Michigan Tech is inviting, engaging, and encourages success."
Learn more about cybersecurity at Michigan Tech!